Browser Based Multi-Factor Authentication
Multi-Factor Authentication (MFA) adds an extra layer of security on top of the basic authentication methods. It requires users to provide multiple proof of their claimed identity prior to being granted access according to their security roles and permissions.
User access can be granted based on two cumulative conditions:
- Something the user knows (login credentials): username and password.
- Something the user controls (a mobile device or email account used to receive a temporary pass code via SMS/E-mail).
When users access the app, they will be prompted to provide the login credentials associated with their FintechOS Platform account. To make sure account access is protected, after the login credentials are provided, a one-time security pass code is sent to the user’s phone (the phone number set in the user account profile) or email address. Once the user enters the code received via the SMS/e-mail, access into the system is granted.
The following authenticator apps have been tested and confirmed as working:
- Microsoft Authenticator
- Google Authenticator
- FreeOTP
Follow the instructions below to set up multi-factor authentication.
1 Create a Browser Authentication Flow
- Log in to the FintechOS Identity Provider admin console.
- Select your FintechOS Platform realm.
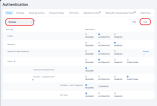
- Select the Authentication blade.
- In the Flows tab, select the Browser based authentication flow and click the Copy button to create a duplicate.
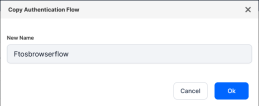
- In the window that opens, assign a name for your new browser authentication flow.
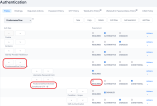
- Open the newly created authentication flow and, in the Forms authentication type, set the Browser - Conditional OTP subflow to Required.
(Optional) Enable Conditional OTP only for specific roles
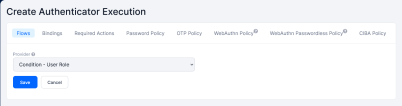
- Open your authentication flow and, in the Forms authentication type, in the Browser - Conditional OTP subflow, click the Actions drop-down and select Add execution.
- In the Create Authentication Execution screen, select the Condition - User Role provider and click Save.
- In the authentication flow window, move the Condition - User Role execution above the OTP Form execution and, from its Actions drop down, select Config.
- In the user authenticator configuration page, add an Alias of your choice and select the Role which will require multi-factor authentication. If you wish to apply multi-factor authentication to all user roles except the provided role, tick the Negate output option.
- On your authentication flow page, in the Forms authentication type, set the Browser - Conditional OTP subflow to Conditional.
2 Associate the Authentication Flow to a Client
- In the Clients blade, open the FintechOS Identity Provider client you wish to enable multi-factor authentication for, such as a Portal or Innovation Studio client.
- In the Settings tab, scroll down to the Authentication Flow Overrides and expand it.
- Set the Browser Flow option to the flow you created earlier and click Save.

Authenticator Reset
Once set up, the multi-factor authentication will be required when a user logs in for the first time. If a user loses access to the authenticator app or needs to reconfigure for various reasons, a FintechOS Identity Provider administrator must log in to the administration console and either:
- Delete the created authenticator
or
